How do web browsers work?
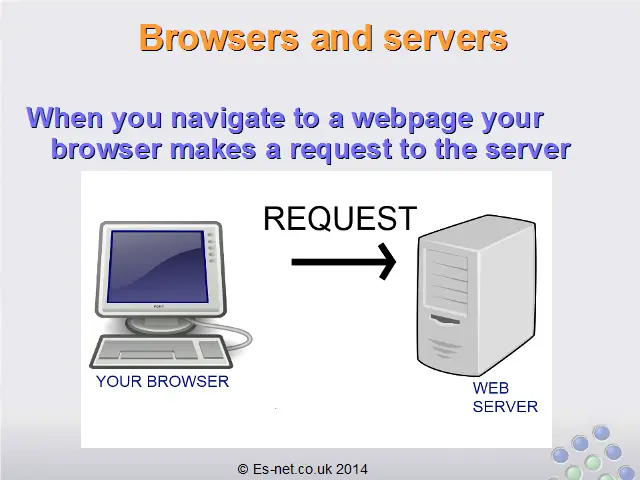
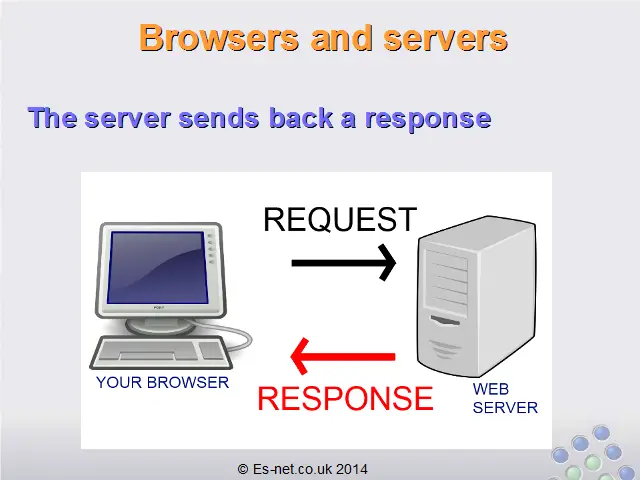
 When you navigate to a website, your browser makes a request to the server that hosts the website.
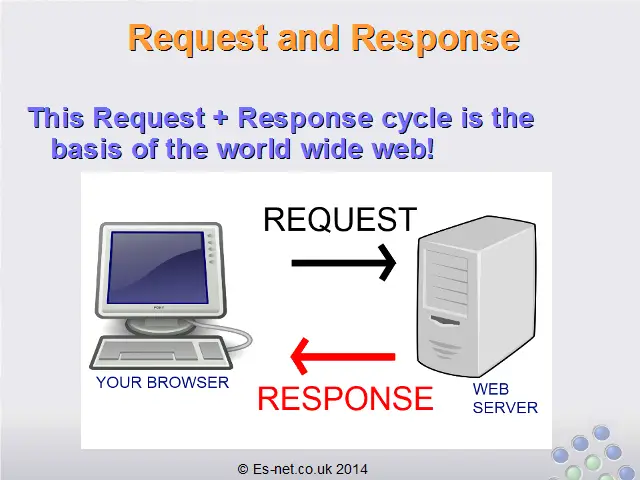
When you navigate to a website, your browser makes a request to the server that hosts the website.Depending on what is contained in that request the server sends back different content in the response.This request/response cycle is the basis of all websites.You can see this happen when you navigate to a page – your browser shows an icon indicating that it has sent a request and is waiting for a response.
For example, in Google Chrome:
You can see in these images that the spinning circle is the way the browser indicates it is waiting for a response from the server. In the second image you can see that it has received some data: in this case, the title of the website which begins “Welcome to Facebook…”. However, it hasn’t yet fully received the entire response so it continues to show the spinning circle.
(This is similar to how other browsers, such as Internet Explorer or Firefox operate.)
The responses change depending on what is happening as you browse. For example, when you first load a website the server will send the first page: often a login page.
When you enter your login details the browser sends another request. This request contains extra data: your username and password. Now the server knows you are logged in so it sends a different response – the response it gives to users that are logged in, for example their own profile page.
As you continue interacting with the website you send more requests to the server, and the server sends back more responses.
Next time you are browsing websites try and notice when your browser makes a request and recognise the responses coming back from the server.
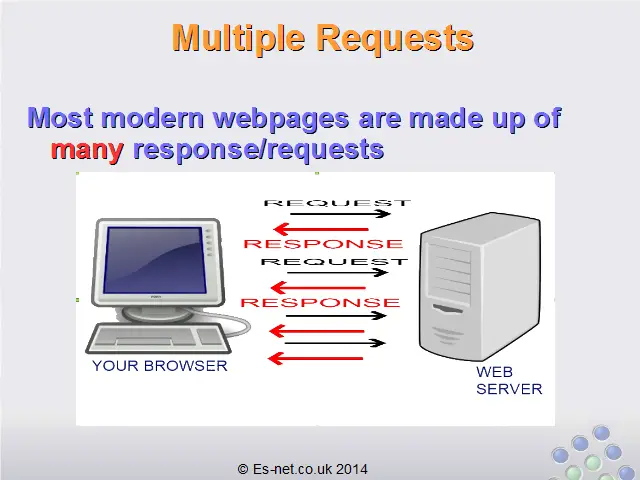
Multiple Request/Responses
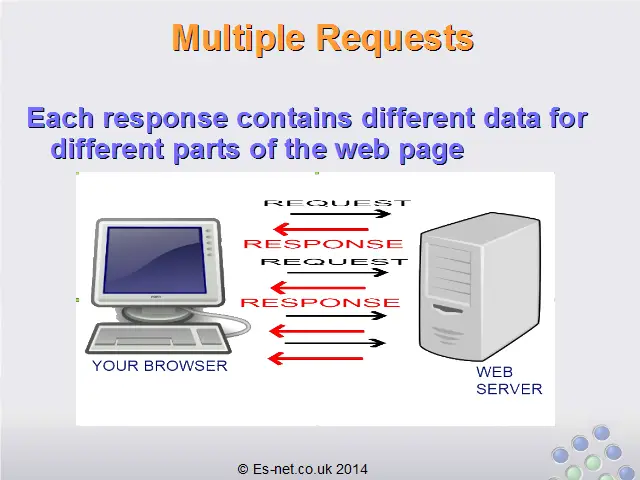
Most modern websites require many requests and responses to load a single page. This is because modern websites are very complex and there are a lot of parts that must come together to form each page. As we go through this course we will learn more about each of these parts, but for now just remember this: each time you load a page your browser makes many requests, and the server sends many responses.
What is in a Response
The response from the server can contain a large variety of data: image data, HTML, JavaScript, CSS, or many other data types.
Sometimes these are even combined: perhaps the server sends HTML, CSS and JavaScript all together in a single response.
Again, we will understand more about each of these types of data as we proceed through the course.
For now the most important thing to understand is that when you view a web page you are viewing a ‘conversation’ between your computer and the internet server. Your computer comes up with part of the conversation via requests and the server finishes the conversation with responses. Try and see this back-and-forth conversation happening as you browse the internet – it will help your understanding the rest of the lessons very much!
Comments
Post a Comment