Physicists Unveil First Quantum Interconnect
An international team of physicists has found a way to connect quantum devices in a way that transports entanglement between them.
One of the unsung workhorses of modern technology is the humble interconnect. This is essentially a wire or set of wires that link one part of an electronic system to another. In ordinary silicon chips, interconnect can take up most of the area of a chip; and the speed and efficiency with which information can travel along these interconnects, is a major limiting factor in computing performance.
So it’s no wonder that physicists and engineers are creating new generations of interconnect that will become the backbone of information processing machines of the future.
One of the most promising forms of number crunching is the quantum computer and its various associate quantum technologies, such as quantum communication, quantum cryptography, quantum metrology, and so on.
Physicists have made great strides in building proof-of-principle devices that exploit the laws of quantum physics to perform feats that would be impossible with purely classical mechanics. And yet a significant problem remains. These devices must work in isolation since nobody has perfected a way of joining them together effectively.
Today, that changes thanks to the work of Mark Thompson at the University of Bristol in the U.K. and a few pals around the world. These guys have built and tested a quantum interconnect that links separate silicon photonic chips and carries photons and, crucially, entanglement between them.
Quantum interconnect is a tricky proposition because of the fragile nature of entanglement, the bizarre way in which quantum particles share the same existence, even when they are far apart.
However, this state is extremely brittle — sneeze and it disappears. So quantum interconnect must preserve entanglement while transporting it from one place to another.
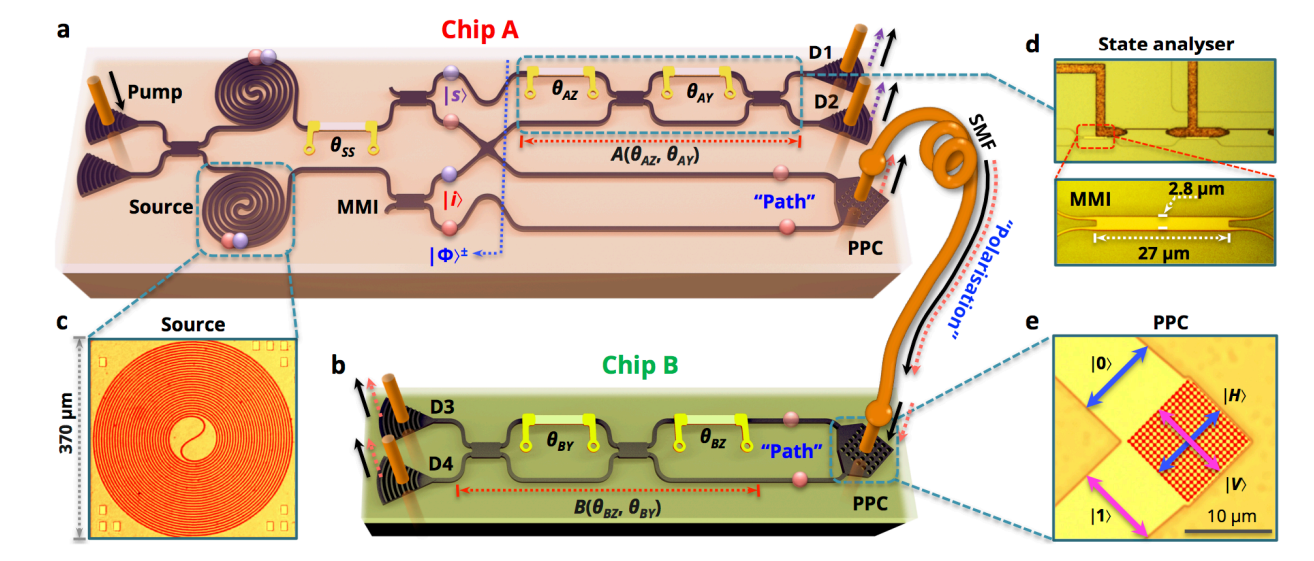
Thompson and co do this using a simple optical fiber and a clever quantum trick. Their silicon chips have two sources of photons that travel along photonic channels that overlap. When photons meet in the region of overlap, they become entangled and then carry this entanglement along separate paths through the device.
The role of the quantum interconnect is to transmit the photons to another chip where they retain their path-encoded entanglement. But how can this be done when the interconnect consists of a single path along a fiber?
The trick that Thomson and pals have perfected is to convert the path-entanglement into a different kind of entanglement, in this case involving polarization. They do this by allowing the path-entangled photons to interfere with newly created photons in a way that causes them to become polarized. This also entangles the newly created photons, which pass into the optical fiber and travel to the second silicon photonic chip.
The second chip reverses this process. There, the polarized-entangled photons are converted back into the path-entangled variety which then continue into the device as if they had come directly from the first chip.
The team has experimented with this proof-of-principle device and show that the entanglement is preserved throughout. “We demonstrate high-fidelity entanglement throughout the generation, manipulation, interconversion, distribution and measurement processes, across two integrated photonic circuits, successfully demonstrating the chip-to-chip quantum photonic interconnect,” they say.
It’s not perfect of course. Thompson and co admit they need to reduce the losses in the machine. But they say all this can be improved in future by optimizing various aspects of the design.
Overall, that’s an important step forward. Quantum interconnect is an enabling technology that should help to make possible a wide variety of new quantum devices that require different quantum subsystems to be linked together.
Ref: arxiv.org/abs/1508.03214 : Quantum Photonic Interconnect
Comments
Post a Comment